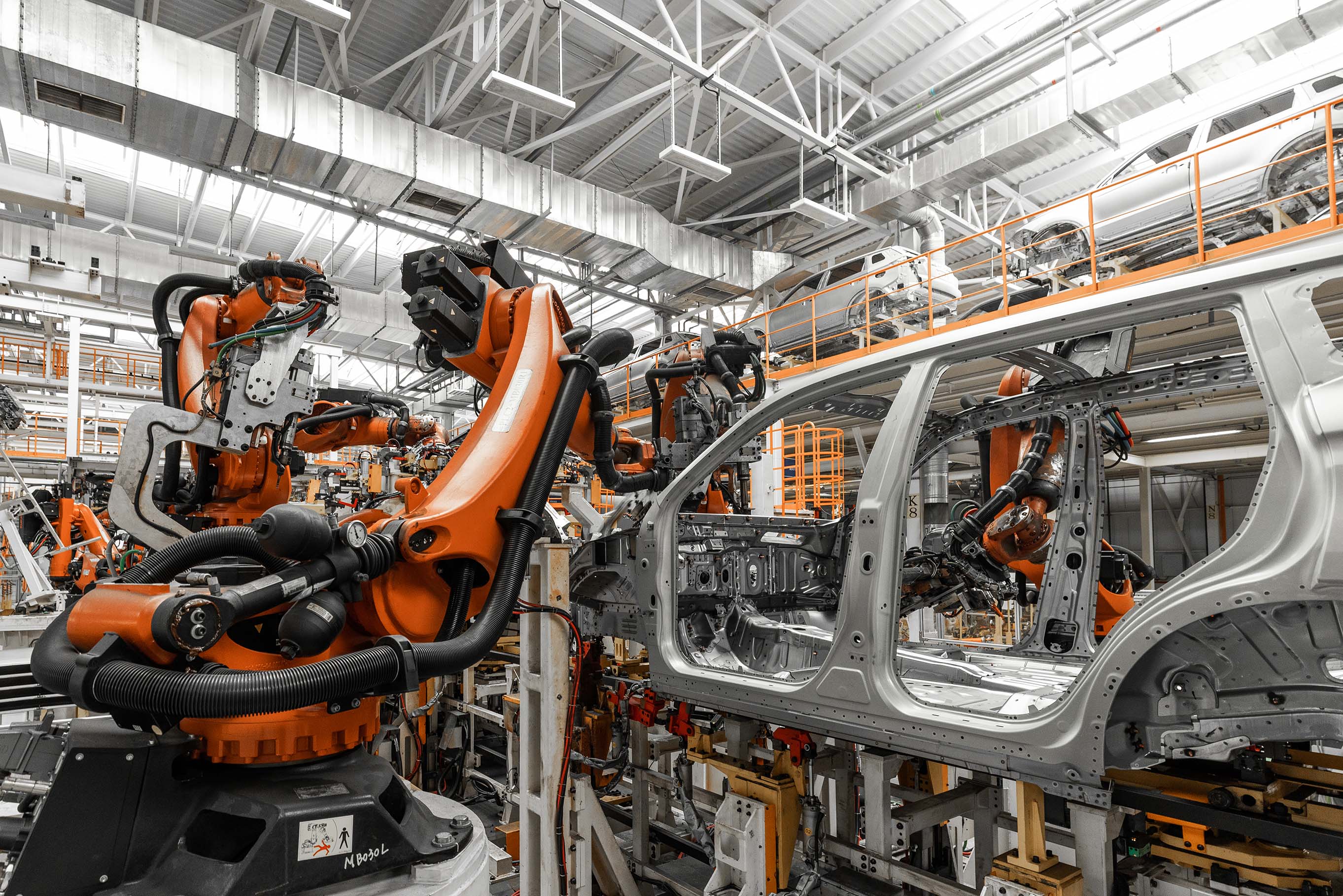
Industrial Cyber Security (OT)
OT and ICS Compliance Based on IEC 62443 and NIS2 Requirements.

Cyber security is no longer optional for connected industrial machinery and OT systems: it is a critical business necessity. We help protect critical assets through advanced testing and proactive risk reduction.
AC&E’s technical expertise
AC&E is a Technical Partner of ISA SECURE. We support our clients with accredited Risk Assessments in compliance with ISA/IEC 62443-3-2.
We also perform accredited Vulnerability Assessments and Penetration Tests, ensuring advanced protection of connected industrial systems and machinery in OT environments.
ISA Secure
Technical Member
ISA Membership
Core cyber-services
For manufacturers of connected industrial machinery and OT systems, cyber security is a strategic priority.
The services offered by AC&E’s Cyber Security Division include:
Risk Assessment
ISA SECURE accredited risk assessments, in compliance with ISA/IEC 62443-3-2
Vulnerability Assessment (Gap Analysis)
A thorough examination of systems to identify potential weaknesses that could be exploited.
Penetration testing
Simulated cyberattacks to evaluate system resilience and uncover critical vulnerabilities.
Technical training
Hands-on training in industrial cyber security to help your organization defend against threats and ensure safe, compliant operations.
Who we support
Cyber security assessment and compliance support for connected electrical and electronic equipment, addressing secure design, risk analysis, and regulatory requirements.

Machinery manufacturers
Cyber security assessment and compliance support for connected electrical and electronic equipment, addressing secure design, risk analysis, and regulatory requirements.
End User (asset owner)
Support for OT cyber security in industrial machinery and plants, including risk assessment, IEC 62443 compliance, and integration of security measures into industrial systems.
Components & products
Cyber security evaluation of products covering vulnerability assessment, compliance verification, and alignment with international cyber security requirements.
All the steps of the process we do
A structured overview of our cybersecurity process, outlining each step from initial assessment to final validation and ongoing monitoring.
Engineering services policy and procedures technical interview
Assessment of OT security policies, procedures, and engineering practices to identify gaps, risks, and alignment with industrial cybersecurity standards.
Risk Assessment IEC 62443-3-2
Structured OT risk assessment based on IEC 62443-3-2 to evaluate threats, vulnerabilities, and potential impacts on industrial processes.
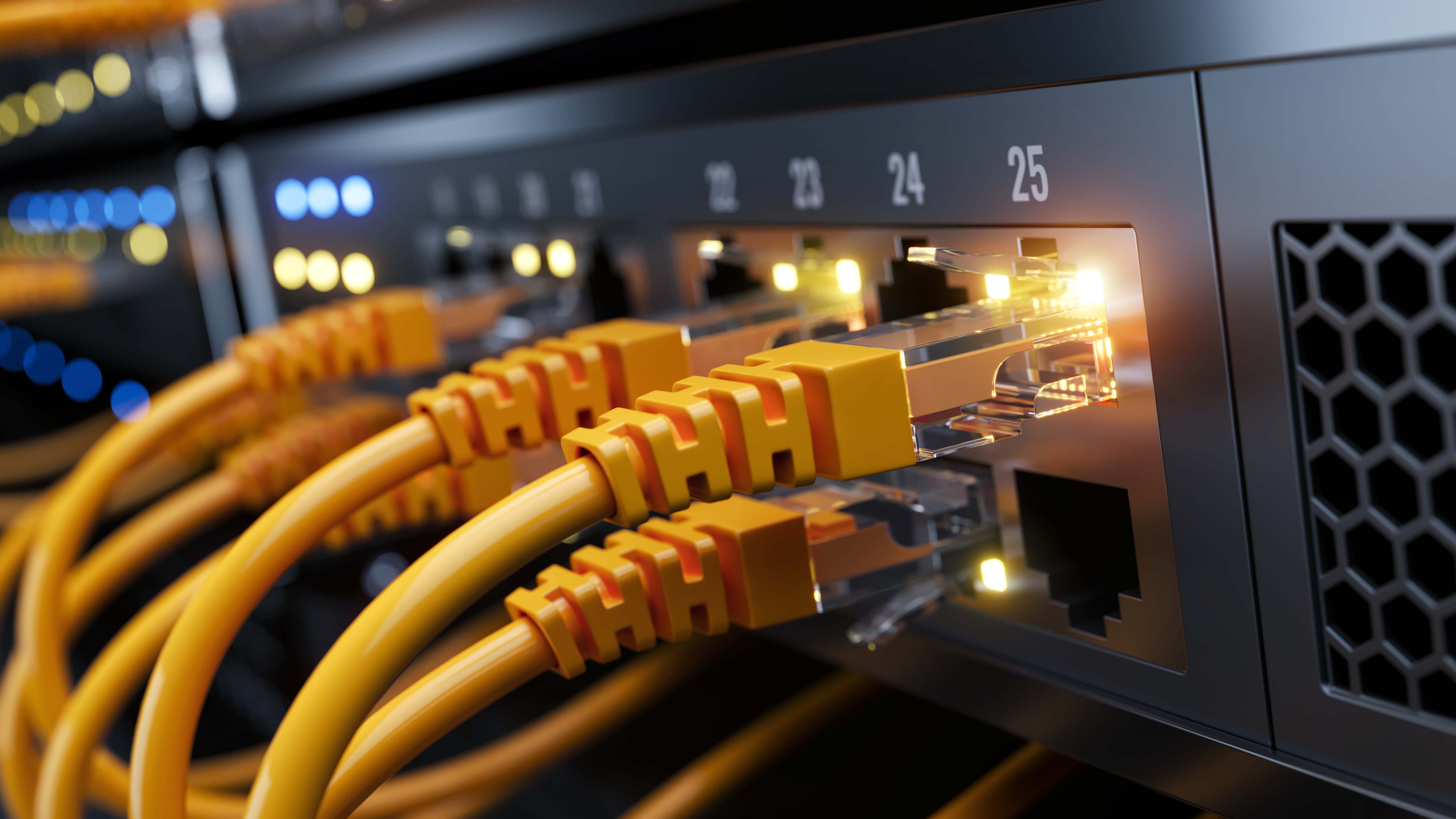
OT network topology mapping and analysis
Detailed mapping and analysis of OT network architecture to identify critical assets, trust zones, and potential security weaknesses.
MES, ERP, and SCADA systems integration
Security-focused evaluation of integrations between MES, ERP, and SCADA systems to ensure secure data flows and reduced attack surfaces.
Protocol scanning and analysis
Inspection and analysis of industrial communication protocols to detect insecure configurations, anomalies, and unauthorized interactions.
Traffic analysis and scanning
Monitoring and analysis of OT network traffic to identify suspicious behavior, malicious patterns, and operational security risks.
Vulnerability Assessment (VA)
Identification and evaluation of vulnerabilities in OT assets, systems, and configurations with minimal impact on operational continuity.
Penetration testing (pen testing or ethical hacking)
Controlled security testing of OT environments to safely simulate real-world attacks and uncover exploitable weaknesses.
OT backup policy implementation verification
Review and validation of OT backup strategies and recovery procedures to ensure resilience against cyber incidents and data loss.
IEC 62443 GAP Analysis Report and NIS 2 GAP Analysis Report
Comprehensive gap analysis against IEC 62443 and NIS2 requirements to measure compliance and define remediation priorities.
Report on the Organization’s Maturity Level
Evaluation of the organization’s OT cybersecurity maturity, governance, and operational capabilities against NIS2 or NIST framework.
OT Security Solutions
Design and recommendation of tailored OT security solutions to protect industrial systems, networks, and critical infrastructure.
Regulatory Cyber compliance
AC&E supports companies in aligning technical, organizational, and regulatory requirements to ensure compliant and secure market access.
Machinery Regulation (EU) 2023/1230
Compliance support for the new Essential Health and Safety Requirements (EHSR) related to software integrity and protection against corruption or malicious interference.
Key focus areas:
- EHSR 1.1.9 – Protection against corruption and cybersecurity threats
- EHSR 1.2.1 – Safety and reliability of control systems
- Secure software architecture and validation
- Protection against unauthorized access and manipulation
- Risk assessment of connected machine functions
Applicable technical standards:
- EN 50742 – Cybersecurity for machinery
- EN IEC 62443 – Industrial automation and control system security
AC&E supports manufacturers in integrating cybersecurity into machine design to ensure compliance with Regulation (EU) 2023/1230 and future-ready product safety.
CRA (Cyber Resilince Act) & RED
Compliance support for products with digital and radio functionalities placed on the EU market.
Scope of application:
- Products with Wi-Fi, 5G, Bluetooth, and radio communication modules
- IoT and connected industrial devices
- Wireless control and communication systems
Key cybersecurity requirements:
- Secure by design and secure by default principles
- Protection against unauthorized access and data manipulation
- Vulnerability management and software update mechanisms
- Risk assessment of digital and communication interfaces
Applicable technical standards:
- EN 18031 – Harmonized cybersecurity standard under RED
- ETSI EN 303 645 – Baseline security requirements for consumer IoT
AC&E assists manufacturers in aligning product design, documentation, and testing with the Cyber Resilience Act (CRA) and the Radio Equipment Directive (RED) cybersecurity provisions.
NIS 2
New EU directive aimed at strengthening the security of networks, information systems, and critical infrastructure across essential sectors.
How Organizations Can Prepare for Future Challenges
With the introduction of Legislative Decree 138/2024, cyber security is no longer optional—it has become an absolute priority for companies.
The NIS2 directive sets out strict new requirements that demand swift and strategic action.
Exporting to North America
Our solutions to ensure compliance, data protection, and defense against cyber threats.
Cyber Risk Reduction
For 25 years, AC&E has been the strategic partner for companies exporting machinery and industrial equipmentto North America, offering a comprehensive package tailored to the U.S. market including cybersecurity.
In addition to being a recognized Field Evaluation Body in the United States, we are also an ISA SECURE Technical
Partner and can support you in achieving compliance with NEC 2023 and NFPA 79, section 4.10.
IAS ACCREDITED
ISA Secure Technical Partner
Certified laboratories
AC&E laboratories, ISO/IEC17025 accredited by PJLA (Accreditation #113455)
Accelerated time to market
Faster certification process, significantly reducing the time required to make products compliant and ready for global markets.
Worldwide Certifications
AC&E offers globally-recognized certifications, ensuring products comply with local regulations
Inspectors located globally
Local support for audits and certifications, ensuring a fast service that complies with international regulations.
Mobile Testing Laboratory
AC&E operates accredited laboratories (ISO/IEC 17025) offering certified testing services to support product compliance across international markets.
ISO/IEC 17025
AC&E is an ISO/IEC 17025 PJLA accredited laboratory, accreditation number #113455.
Internationally recognized
Our certified test reports are accepted by regulatory authorities worldwide.

Get in touch with one of our experts
Connect with our team to transform technical complexity into clear, confident decision-making for your next project.
